What is Cyberstanc Vortex Threat Detection?
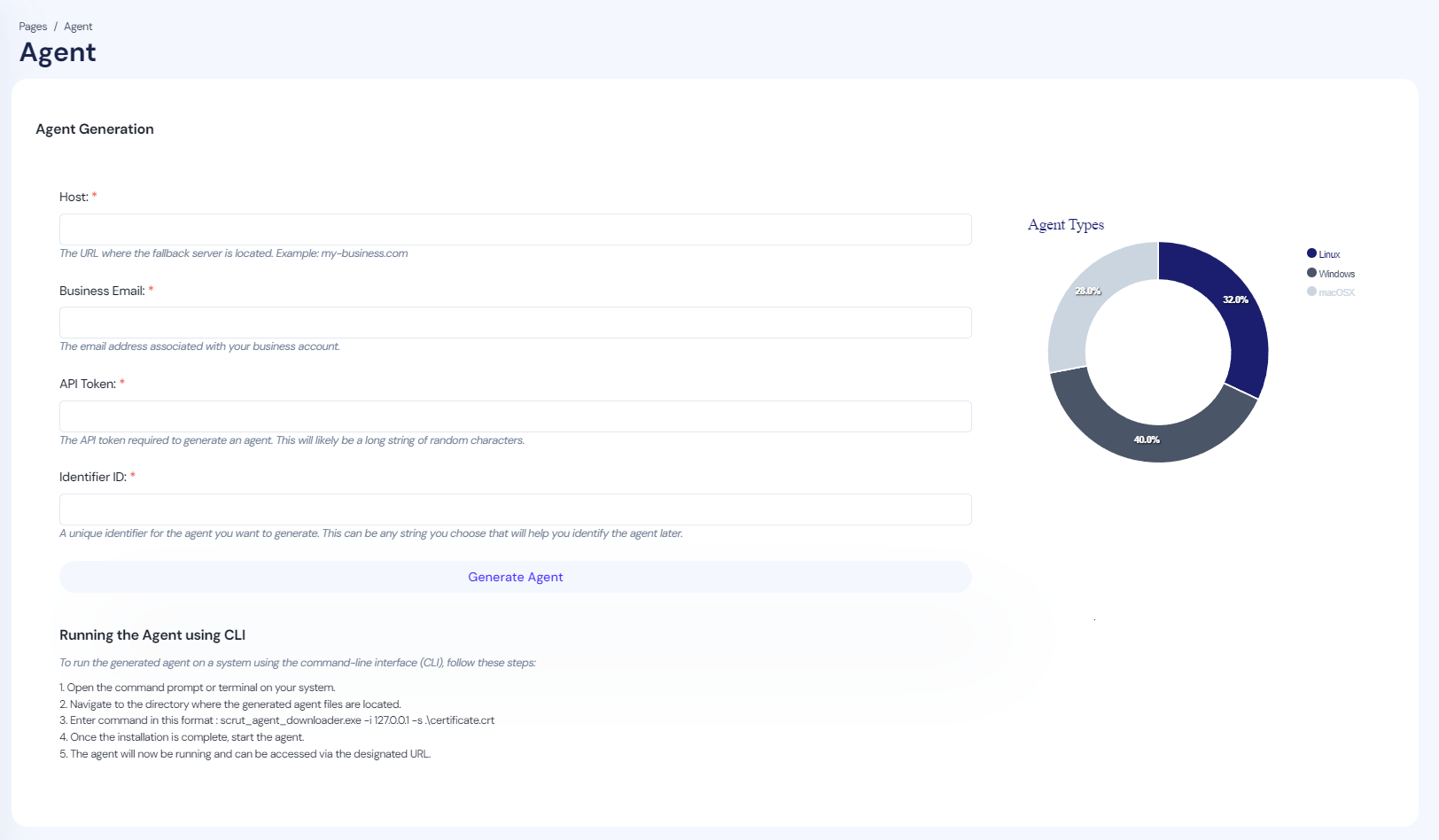
Cyberstanc Vortex is designed to enhance the existing frameworks, tools, and techniques for secure data transfer between secure networks. By utilizing Simulation Intelligence and Signature-less detection capabilities, it aims to bridge the gaps and overcome limitations present in current solutions. With its "Report, Remove, and Sanitize" feature, Cyberstanc Vortex is designed to provide comprehensive protection and ensures the secure transfer of data.
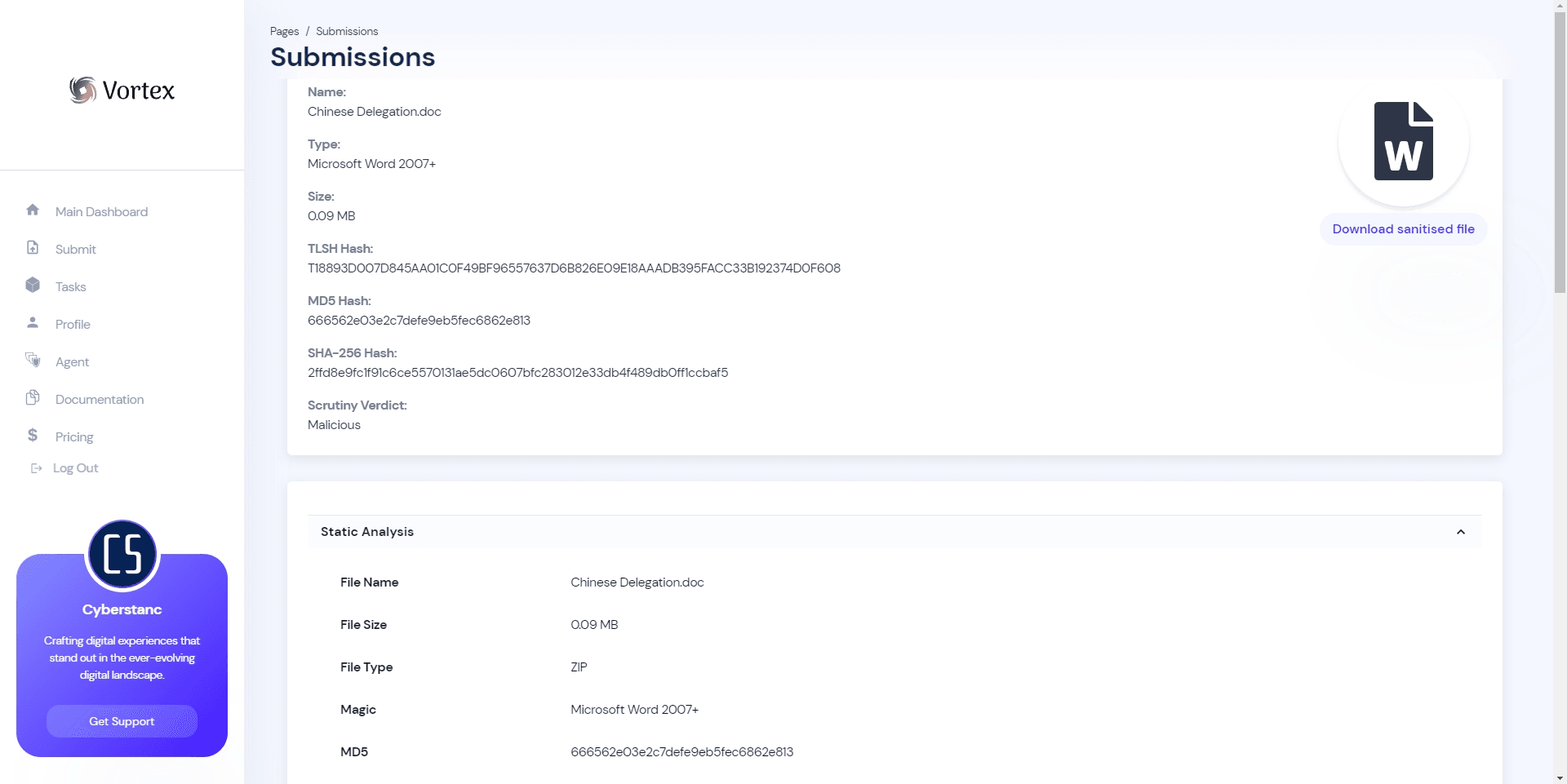
Cyberstanc Vortex boasts strong detection accuracy that surpasses traditional anti-virus solutions. By reducing the number of artifacts that need to be sandboxed, it helps to save time and resources while minimizing false positives. Through the examination of metadata, file structure, and relationships between files, Cyberstanc Vortex employs simulation intelligence to identify threats. This actionable intelligence provides security teams with detailed information about the nature and behavior of the detected malware, going beyond the simple flagging of files as suspicious.
Supporting transparency and accountability, Cyberstanc Vortex features detection mechanisms that are designed and built with a strong emphasis on transparency, to ensure that organizations can trust the accuracy of the results.
Vortex also offers a prototype framework for data sanitization, providing endpoint, network, email, and storage protection. It covers various grey areas that attackers often target, including highly obfuscated and real-world malware techniques such as macro malware, VBA, VBS, PowerShell, DOCx, and Calendar files.
The platform also offers advanced malware simulation of files up to 1GB, providing evidence-based detection and revealing the true nature of the files. While providing robust protection against malware threats, Cyberstanc Vortex maintains a no-data acquisition policy, prioritizing user privacy.
Categories & Use Cases
Media
1 / 4
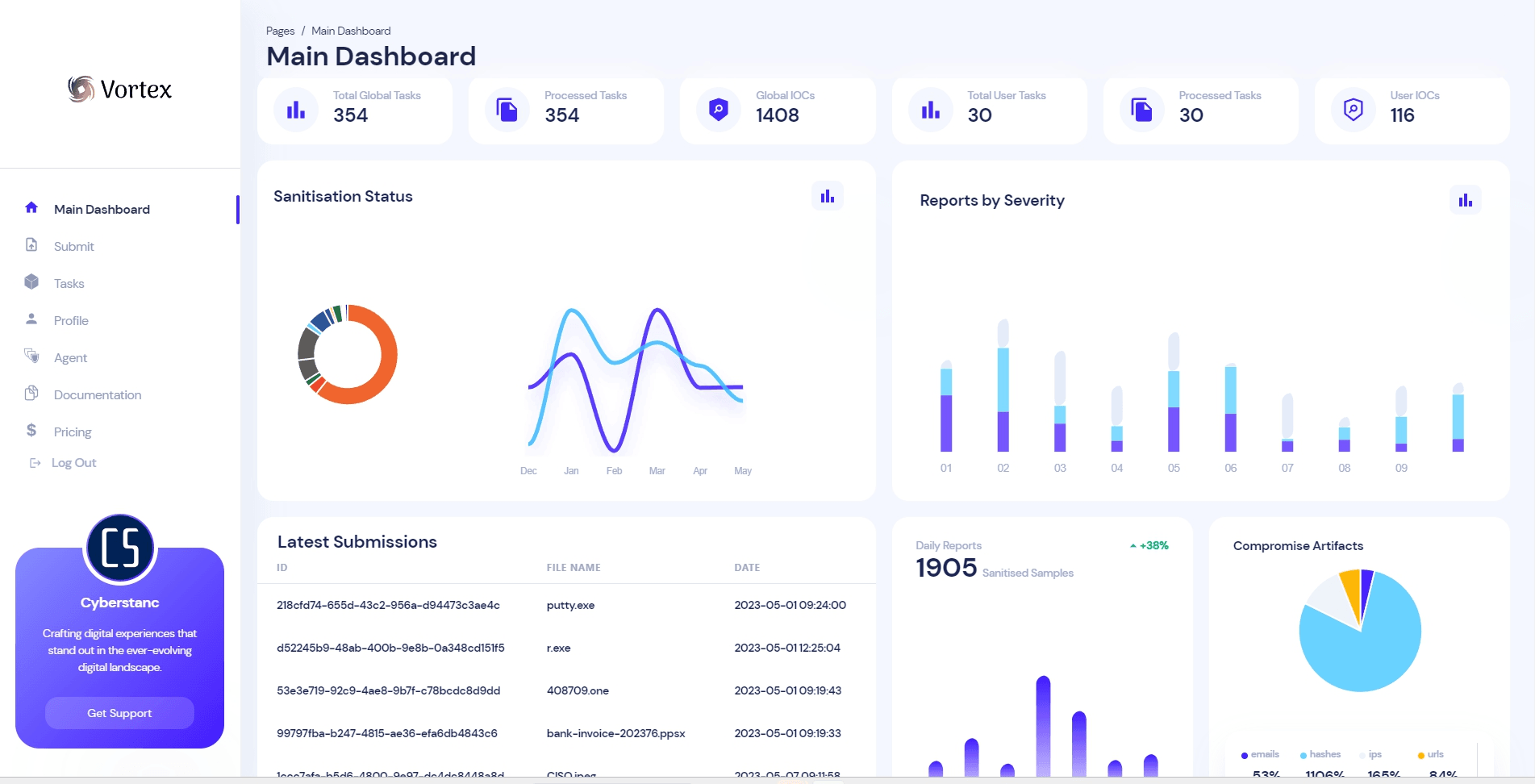
Screenshot of Vortex comprehensive dashboard