What is IDM365?
IDM365 Identity and Access Management Solution is designed to assist organizations in efficiently managing and governing user access to systems and resources. According to the vendor, this solution automates and centralizes the provisioning process, streamlining onboarding, offboarding, and access modification tasks. IDM365 is said to be suitable for businesses of various sizes, from small enterprises to large corporations. It caters to a wide range of professionals and industries, including IT administrators, security professionals, compliance officers, human resources professionals, and finance professionals.
Key Features
Controlled Sharing of Information: According to the vendor, IDM365 enables the implementation of granular access controls based on user roles and permissions to prevent unauthorized sharing of sensitive information.
Secure Audit Trails & On-Time Reporting: The vendor claims that IDM365 automatically generates reliable audit logs for all access requests, authorization decisions, and administrative changes, ensuring compliance with regulatory requirements.
Secure Procedures for Access to High-Risk Systems and Databases: IDM365 is said to streamline the management of access to high-risk systems and databases by implementing robust authentication and authorization processes to prevent unauthorized access.
Complete and Immediate Removal of Access: The vendor states that IDM365 allows for the prompt revocation of user access across all resources, improving security by ensuring the immediate removal of access to all systems and applications.
Reliable Audit Logs: According to the vendor, IDM365 automatically generates audit logs for all access requests, authorization decisions, and administrative changes, maintaining a detailed record of user access activities for auditing and compliance purposes.
Tighter Security and Sustained Compliance Management: The vendor claims that IDM365 enhances security measures and facilitates compliance through the enforcement of centralized security policies across all users and systems.
Centralized Identification and Authorization: According to the vendor, IDM365 simplifies user management by providing a single point of control for user access across multiple systems, automating user provisioning and access requests.
Approval Workflows: IDM365 purportedly integrates approval workflows to streamline the routing and escalation of access requests, ensuring transparency and accountability in the approval process.
Automated Access Management: The vendor states that IDM365 streamlines the onboarding and offboarding processes by automating user provisioning and deprovisioning, reducing administrative overhead and improving efficiency.
Identity and Access Management (IAM): According to the vendor, IDM365 provides a foundation for information security, compliance with data policies, and governance requirements, enforcing access policies and maintaining a strong defense against inappropriate information access.
Categories & Use Cases
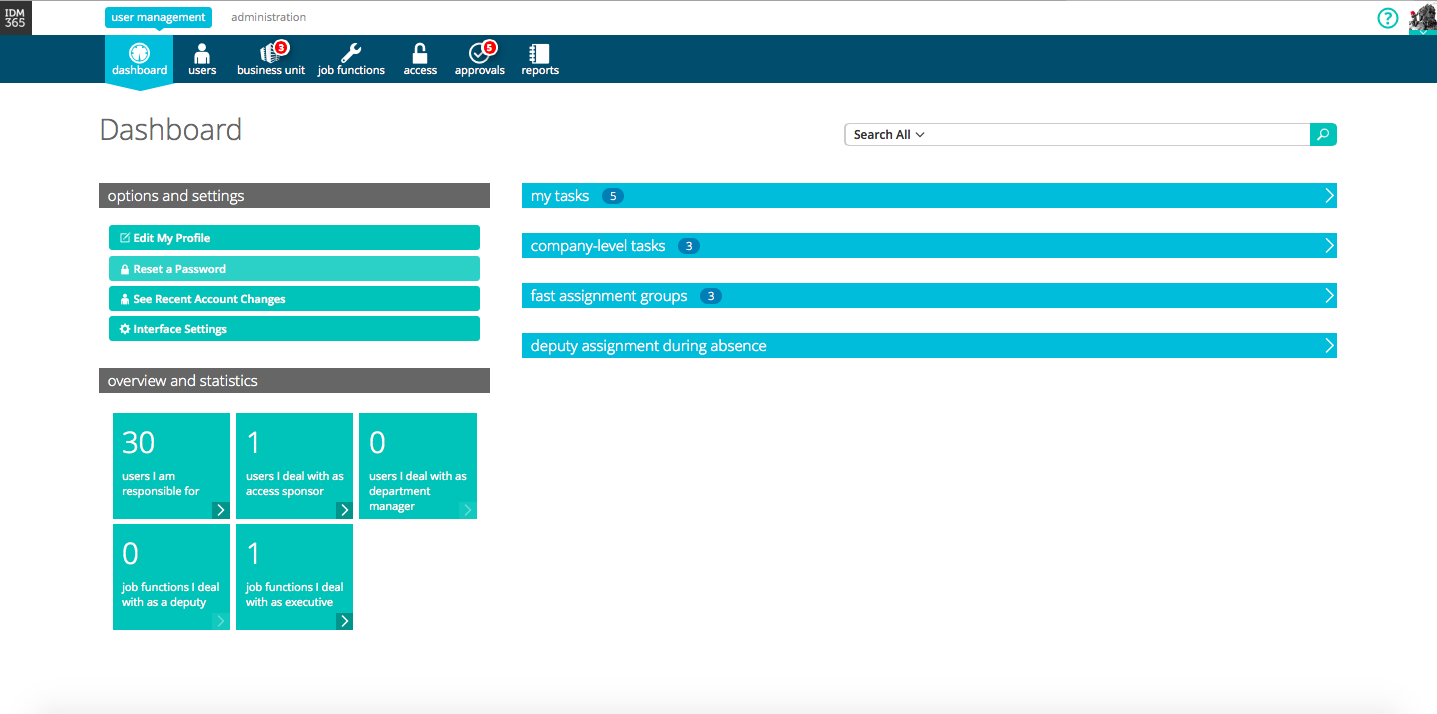
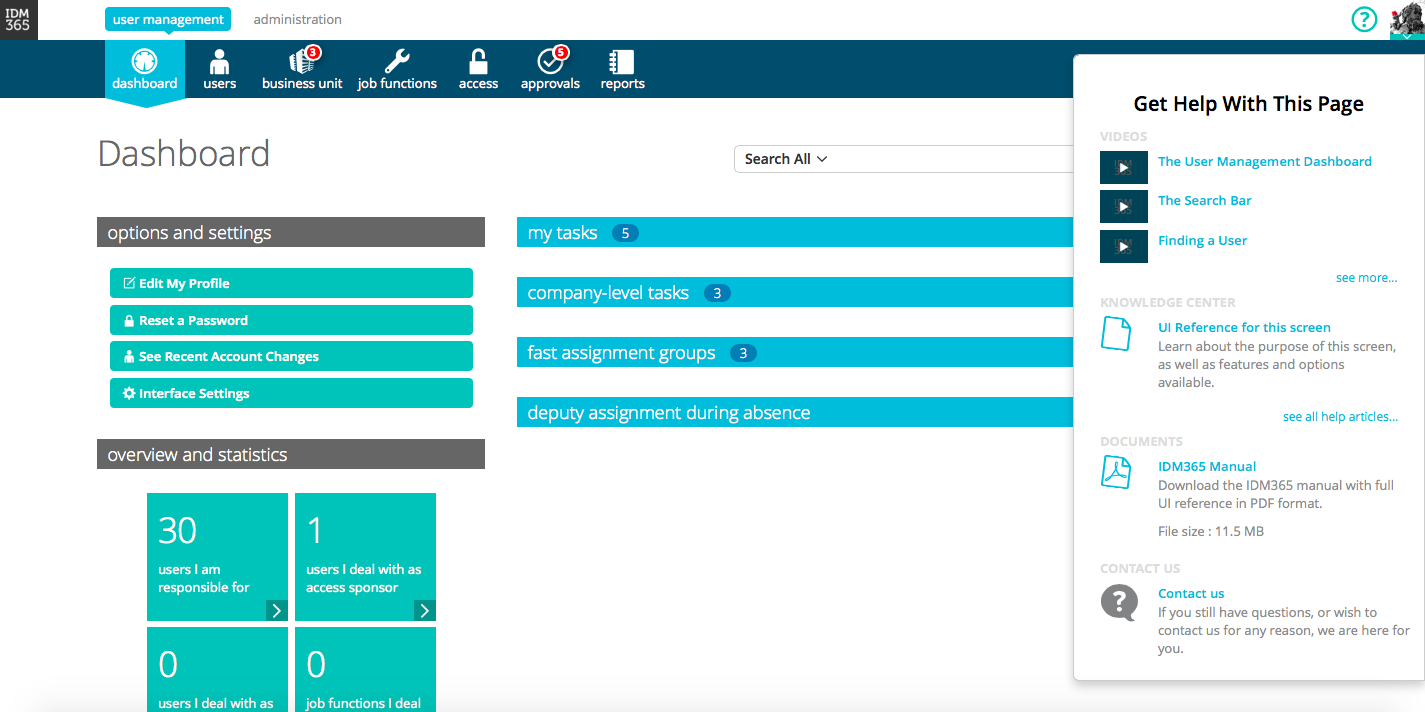
Media
1 / 2