Mandiant Managed Defense - Integration & Protection
Use Cases and Deployment Scope
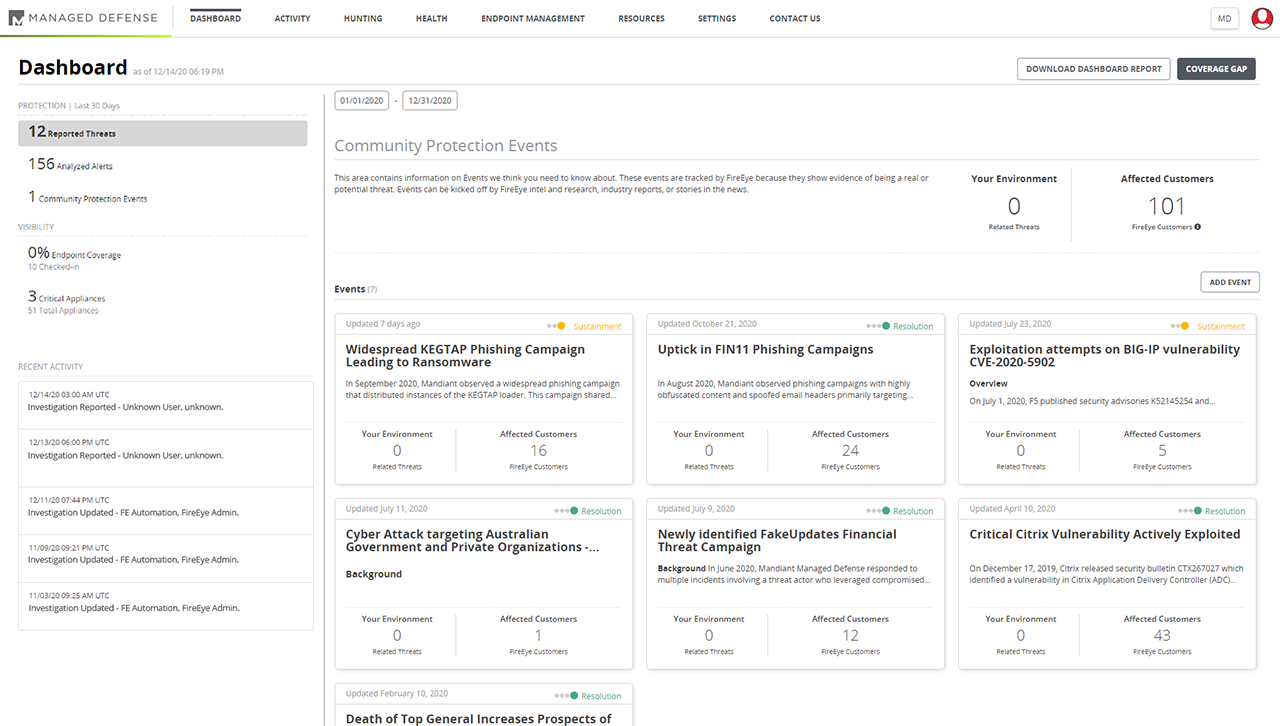
We were looking for Managed Detection & Response solution for our customer as there was issues on clarity of threats , which can not be define Bad & Good by even best technology available in market. MDR services can be a cost effective way to access the necessary detection & response skills and resources without having to recruit, train and retain the internal talent.
Pros
- Integration & Protection-Mandiant provide highest degree of integration with Endpoints, Networks ,email & Cloud and Identity solutions an organization already using
- Strong Protection- Mandiant has best threat landscape technology which provide holistic view of security & Protection.
Cons
- Due to split from FireEye Mandiant no longer can provide its own End Point Protection as part of MDR for customers that want to transition after incident is complete .
- Single remediation response with no-ongoing monitoring
Return on Investment
- Mandiant is strong on automated remediation & rollback
- Predictable Pricing Rapid Response is sold as fixed days term license this takes way risk of hourly billing and runway costs
Alternatives Considered
Microsoft Defender Threat Intelligence