What is SearchInform SIEM?
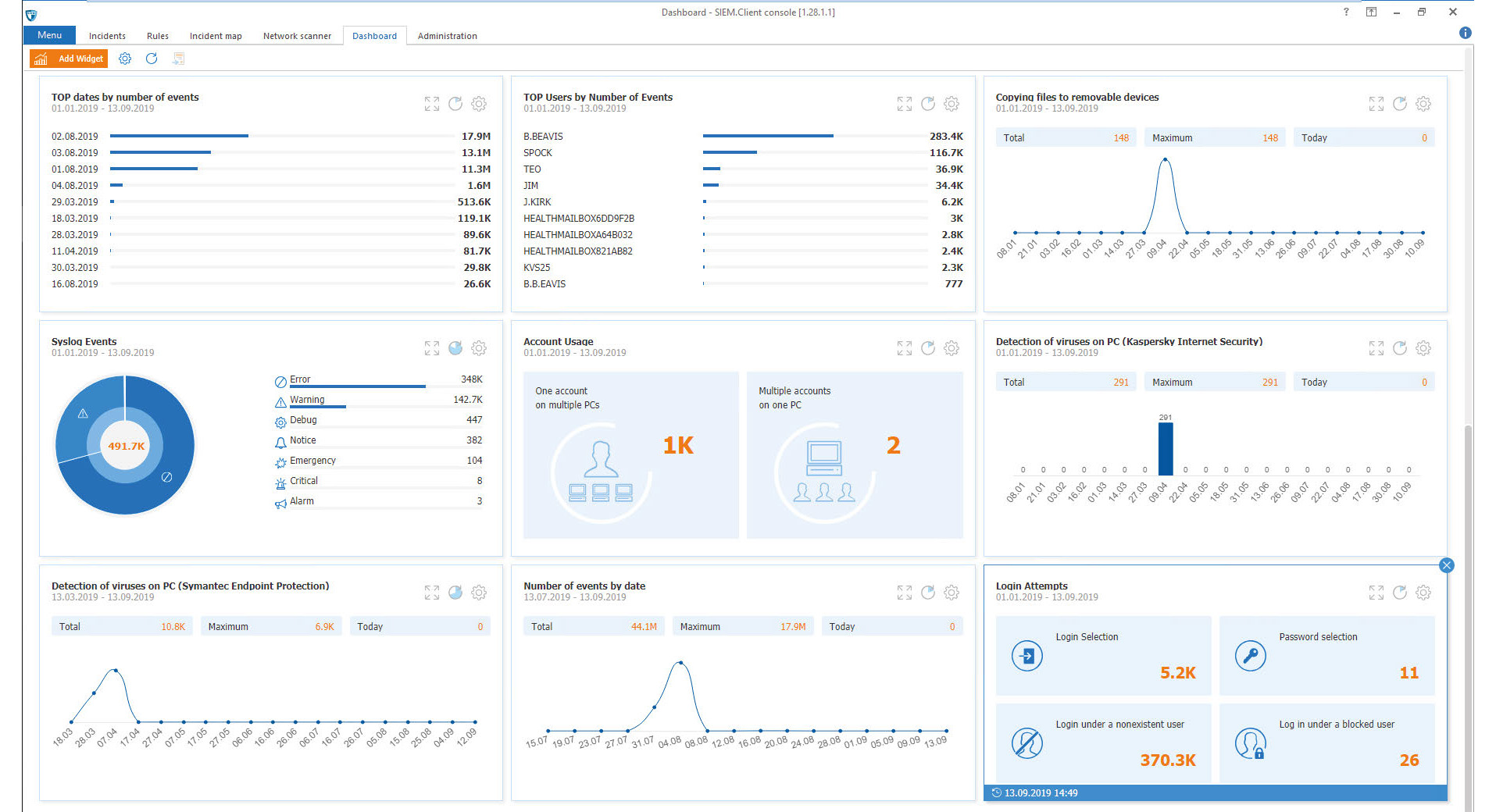
SearchInform SIEM is an out-of-the-box system for collecting and analyzing real-time security events, identifying information security incidents and responding to them. The solution accumulates information from various sources, analyzes it, records incidents and alerts the designated staff being deployed in a few hours.
The SearchInform SIEM reveals:
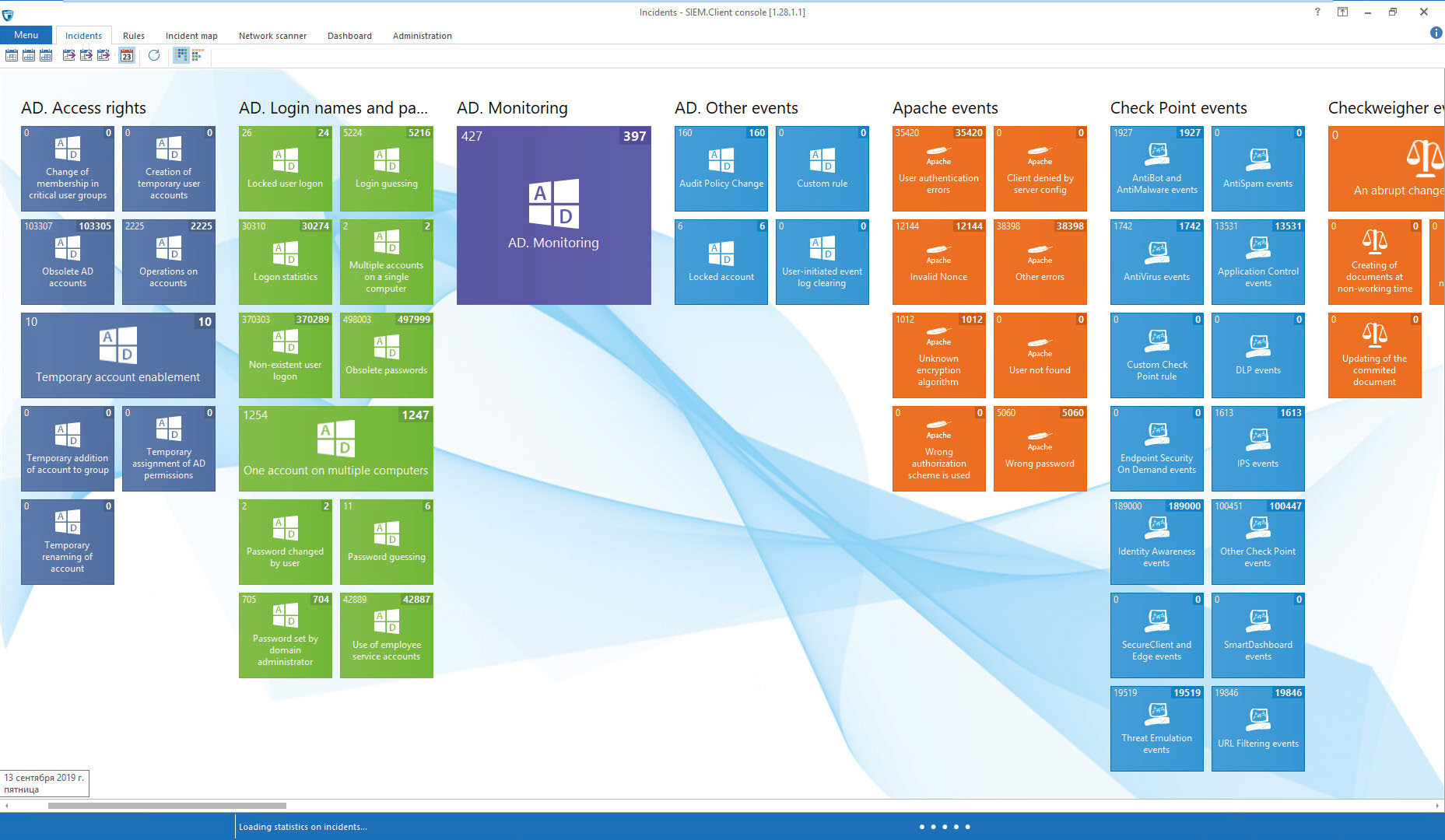
· Virus epidemics and separate infections
· Attempts to gain unauthorized access to data
· Account password guessing
· Active accounts of dismissed employees that had to be deleted
· Hardware configuration errors
· Permissible operating temperature abuse
· Data removal from critical resources
· Use of corporate resources during off-duty time
· Virtual machines and snapshots removal
· Connecting new equipment to IT infrastructure
· Group policy changes
· TeamViewer usage, remote access to corporate resources
· Critical events in protection systems
· Errors and failures in information systems
Advantages:
· Out-of-the-box analytics: the system comes with a set of ready-made rules and incorporates the previous experience of working with companies from all sectors of the economy.
· Incident management. It's possible to create an investigation based on one or more incidents.
· Quick implementation without a need for a lengthy pre-configuration (software can be put into operation in just one day with instant results).
· Easy to use: the program can be handled by an employee with no particular IT skills or knowledge of programming languages – none are required to create correlation and cross-correlation rules.
· Low hardware requirements, transparent licensing, comfortable cost of ownership.
Categories & Use Cases
Media
1 / 2